Setting up a Policy-Based IPsec VPN between a Palo Alto PA-200 and pfSense
As part of an ongoing home network project, i’m trying to set up an IPsec VPN mesh between different sites – e.g. my own home, family home and VPS hypervisor located in an offsite datacentre. The reasoning behind this?
- Because I can and because it’s fun!
- To allow for easier resource sharing and remote diagnosis.
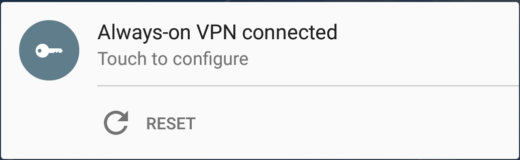
- To allow for an always-on VPN for mobile devices, both at home and away.
Being a home network, none of the equipment is particularly Enterprise grade, with the exception of the PA-200 firewall I have. This introduces a bit of a problem as route-based IPsec VPNs tend only to be supported on Enterprise-grade equipment (support for VTIs is just starting to come in on StrongSwan but has absolutely no documentation right now). Thus, I have to use a policy based VPN, which has limitations but will work for this specific use case.
Of course, any networking topic is greatly aided by a Visio diagram so here’s what i’m trying to achieve;
Palo Alto Configuration
These instructions are based off the web interface, but should be easily adaptable to the terminal. They also assume you’re running PAN-OS 6, but it’s likely similar for other versions.
- Add an IKE Gateway for Phase 1 negotiation via Network > Network Profiles > IKE Gateways > Add.
- Set a friendly name for the remote gateway.
- Select the interface it will originate from. This should be your WAN or Untrust interface.
- Select the IP address on the interface that it will originate from.
- Set Peer IP Type static.
- Set Peer IP to the IP of the remote gateway (2.2.2.2).
- Select Authentication as Pre-shared Key.
- Set a strong, random Pre-shared Key.
- Set Local Identification to IP address, enter your WAN/Untrust IP (1.1.1.1).
- Set Peer Identification to IP address, enter your gateway’s WAN IP (2.2.2.2).
- Click OK.
- Adjust the default IKE Crypto profile via Network > Network Profiles > IKE Crypto.
- Set DH Group to group2 only.
- Set Encryption to 3des only.
- Set Authentication to sha1 only.
- Set Lifetime to 8 hours.
- Click OK.
- Adjust the default IPsec Crypto Profile via Network > Network Profiles > IPsec Crypto.
- Set IPsec Protocol to ESP.
- Set Encryption to aes256 only.
- Set Authentication to sha512 only.
- Set DH Group to group2.
- Set Lifetime to 1 hours.
- Click OK.
- Add a new Tunnel Interface via Network > Interfaces > Tunnel.
- Click Add.
- Set an Interface Name and optionally number.
- Set the Virtual Router and Security Zone to your desired values. I used the main Virtual Router and a separate VPN Tunnel Security Zone.
- Click OK. Do not set an IP – this is a policy based VPN remember! There are no IPs on the tunnel interface as a result.
- Add an IPsec Tunnel for Phase 2 negotiation via Network > IPsec Tunnels.
- Click Add.
- Set a friendly name.
- Select the Tunnel Interface created in Step 4.
- Set Type to Auto Key.
- Select the IKE Gateway created in Step 1.
- Select the IPsec Crypto Profile credited/edited in Step 3.
- Enable Showing Advanced Options
- Enable Replay Protection.
- On the Proxy IDs tab, add a new Proxy ID. This is an important and often overlooked step when creating a Policy-Based IPsec VPN on Enterprise devices.
- Set a friendly name for the Proxy ID.
- Set the local IP netmask that will be routed (192.168.0.0/16).
- Set the remote IP netmask that will be routed (192.168.1.0/16).
- Set Protocol to Any.
- Click OK Twice.
- Adjust your security zone rules as appropriate and add a static route to the remote subnet (192.168.1.0) via the tunnel interface. You should know how to do this ;)
- Commit.
All done! Now for the pfSense side.
pfSense Configuration
These instructions are also for configuration via the web interface, but with pfSense you don’t really have much choice! They are however based off pfSense 2.2 Alpha as I needed to use this version for proper support under my virtualisation infrastructure, things may be slightly different in other versions. Experienced StrongSwan users should also be able to follow these instructions and adapting them to the StrongSwan configuration.
- Enable IPsec via VPN > IPsec, checking the Enable IPsec option and clicking save.
- Add an IKE Gateway for Phase 1 negotiation via VPN > IPsec.
- Set Key Exchange Version to V1. Palo Alto does not yet support V2.
- Set Internet Protocol to V4.
- Set Interface to the Interface of your external Interface (WAN).
- Set Remote gateway to the IP of the remote gateway (1.1.1.1).
- Set Authentication method to Mutual PSK.
- Set Negotiation mode to Main (Aggressive is less secure).
- Set My identifier to IP address and the External IP (2.2.2.2). This must match the Peer Identification set on the Palo Alto device.
- Set Peer identifier to IP address and the IP of the remote gateway (1.1.1.1). This must match the Local Identification set on the Palo Alto device.
- Set the Pre-Shared Key to the same Pre-Shared Key.
- Set Encryption Algorithm to 3DES.
- Set Hash Algorithm to SHA1.
- Set DH key group to 2 (1024 bit).
- Set Lifetime to 28800 seconds.
- Set NAT Traversal to Disable.
- Enable Dead Peer Detection.
- Click Save.
- Add an IPsec Tunnel for Phase 2 negotiation via VPN > IPsec and expanding the Phase 2 entries section underneath your new Phase 1 definition.
- Set Mode to Tunnel IPv4.
- Set Local Network Type to LAN subnet (192.168.1.0/24). This must match the Remote Proxy ID set on the Palo Alto device.
- Set the Remote Network Type to Network and enter the Address. This must match the Local Proxy ID set on the Palo Alto device.
- Set Protocol to ESP.
- Set Encryption Algorithms to AES 256 bits only. Do not set Auto.
- Set Hash Algorithms to SHA512 only.
- Set PFS key group to 2 (1024 bit) only.
- Set Lifetime to 3600 seconds.
- Click Save.
- Click Apply Changes.
Checking Everything is Working
Theoretically as soon as you complete the configuration on the pfSense side everything should start working. To verify this, try pinging the other side of the VPN tunnel, making sure to set the source IP appropriately. For example, from the Palo Alto you’d run;
ping source 192.168.0.1 host 192.168.1.1
If that works, then all traffic should work. On the Palo Alto side, it’s really important that you set the Security Zones and Static Route over the tunnel appropriately!
Verifying Status on the Palo Alto Device
Under Network > IPsec Tunnels check the status indicators for the IPsec tunnel. The first indicator shows phase 2 negotiation, the first indicator shows phase 1 negotiation. You want both of these to be green.
For a more detailed status, you can also run the following commands on the command line;
show vpn ike-sa gateway NAMEOFIKEGATEWAY show vpn ipsec-sa tunnel NAMEOFTUNNEL:NAMEOFPROXYID
The first command should show phase 1 and 2 negotiation, the second command should show tunnel information.
Verifying Status on pfSense
Under Status > IPsec check the Status of the Phase 1 connection, it should be established. Expand the child SA entries section to show the Phase 2 connection. It should show the local and remote subnets.
Conclusion
Hopefully this has helped you get a policy-based IPsec VPN running between a Palo Alto device and pfSense. It’s a shame there’s not greater support for route-based IPsec VPNs in the Open Source world, but I will certainly be watching the addition of VTI support to StrongSwan with great interest. In the mean time, this solution does the job!
If you’re following these instructions, good luck! If you’re still stuck and can’t work out why, Palo Alto have a good page on diagnosing IPsec problems.







I followed this and it partially worked. I can get the tunnel to connect from the pfsense box and the palo sees the connect but the tunnel is red and I can’t ping any devices on the other network behind the pfsense router. it looks like pfsense sees the tunnel so the issue could be on the palo side. My network is this 192.168.20.0/24 is behind the palo and 192.168.2.0/24 is behind the pfsense. How would I go about routing the traffic so I can connect and ping devices on either side?